Accelerated Cell Pages WordPress plugin, with over 100,000 installations, patched a medium severity vulnerability that would permit an attacker to inject malicious scripts to be executed by web site guests.
Cross-Web site Scripting By way of Shortcode
A cross-site scripting (XSS) is among the most frequent sort of vulnerability. Within the context of WordPress plugins, XSS vulnerabilities occur when a plugin has a solution to enter knowledge that isn’t sufficiently secured by a course of that validates or sanitizes consumer inputs.
Sanitization is a solution to block undesirable sorts of enter. For instance, if a plugin permits a consumer so as to add textual content by way of an enter discipline, then it must also sanitize anything that’s enter into that type that doesn’t belong, like a script or a zipper file.
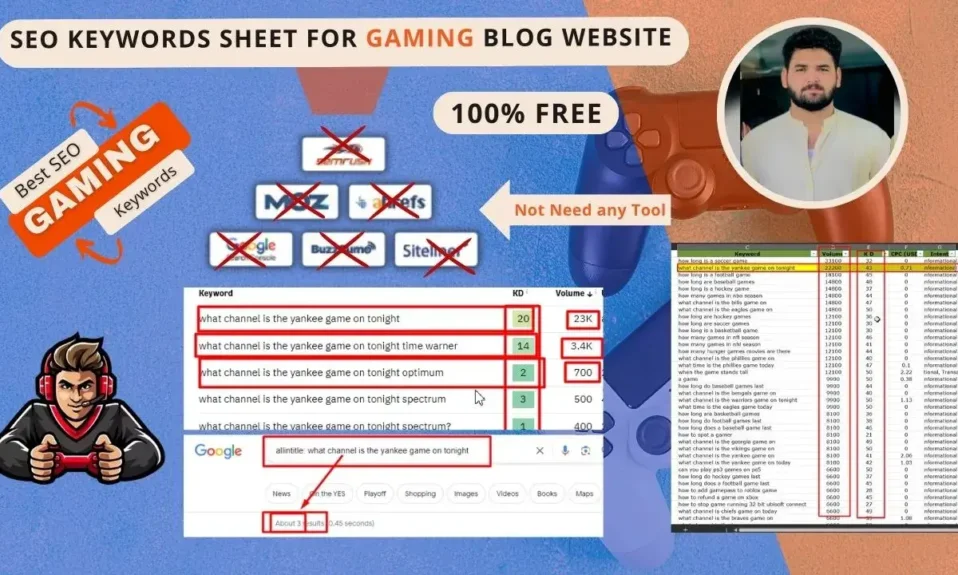
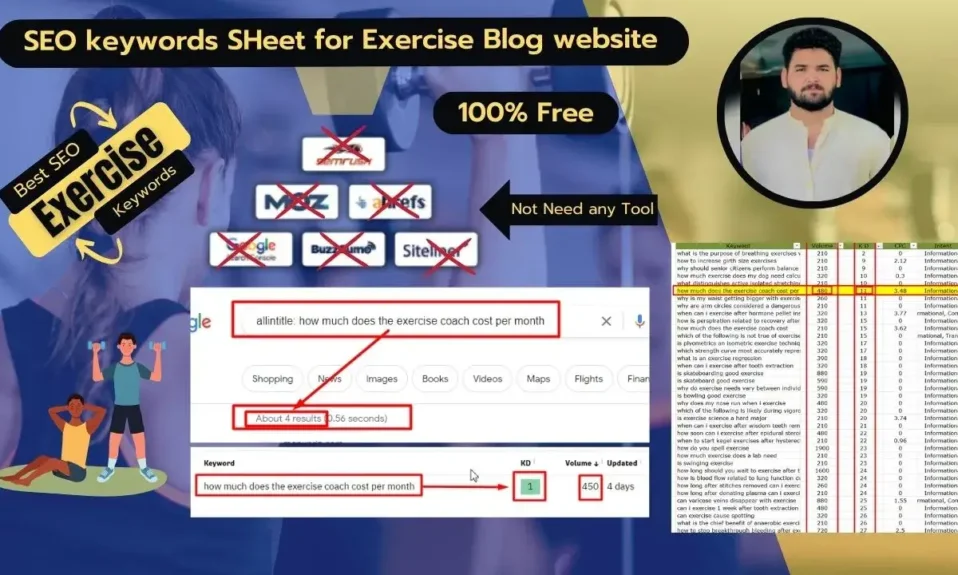
A shortcode is a WordPress characteristic that permits customers to insert a tag that appears like this [example] inside posts and pages. Shortcodes embed functionalities or content material that’s offered by a plugin. This enables customers to configure a plugin by way of an admin panel then copy and paste a shortcode right into a publish or web page the place they need the plugin performance to look.
A “cross-site scripting through shortcode” vulnerability is a safety flaw that permits an attacker to inject malicious scripts into an internet site by exploiting the shortcode operate of the plugin.
In keeping with a report not too long ago printed by the Patchstack WordPress safety firm:
“This might permit a malicious actor to inject malicious scripts, akin to redirects, commercials, and different HTML payloads into your web site which shall be executed when visitors go to your web site.
This vulnerability has been fastened in model 1.0.89.”
Wordfence describes the vulnerability:
“Accelerated Cell Pages plugin for WordPress is weak to Saved Cross-Web site Scripting through the plugin’s shortcode(s) in all variations as much as, and together with, 1.0.88.1 as a consequence of inadequate enter sanitization and output escaping on consumer provided attributes.”
Wordfence additionally clarifies that that is an authenticated vulnerability which for this particular exploit implies that a hacker wants at the least a contributor permission degree as a way to reap the benefits of the vulnerability.
This exploit is rated by Patchstack as a medium severity degree vulnerability, scoring a 6.5 on a scale of 1-10 (with ten being essentially the most extreme).
It’s suggested that customers test their installations in order that they’re patched to at the least model 1.0.89.
Learn the Patchstack report right here:
WordPress Accelerated Cell Pages Plugin <= 1.0.88.1 is weak to Cross Web site Scripting (XSS)
Learn the Wordfence announcement right here:
Accelerated Cell Pages <= 1.0.88.1 – Authenticated (Contributor+) Saved Cross-Web site Scripting through shortcode
Featured Picture by Shutterstock/pedrorsfernandes
#WordPress #AMP #Plugin #Vulnerability #Impacts #Websites